Visa Europe revealed important stats about the usage of Contactless Cards. Poland, Spain and the UK use this payment methd the most, with UK usage growing by 300% year over year.
Visa Europe revealed important stats about the usage of Contactless Cards. Poland, Spain and the UK use this payment methd the most, with UK usage growing by 300% year over year.
The assessment phase is when vulnerabilities are identified and it includes the proper identification of all assets in scope, scanning for vulnerabilities, and reporting the findings.
The organization must implement asset discovery for all technology environments included in the scope of the VM program. An updated CMDB is the preferred way to manage asset data, however, most organizations are unable to consistently maintain such a database. In this regard, VA tools provide different asset discovery capabilities. A VM program should account for changes to the business and an evolving IT environment and consequently, organizations must also connect the VM program to the existing change management processes.
VA should be more frequent than remediation, but in most cases, it doesn’t need to be drastically more frequent; PCI DSS 11.2 and 6.1 indicate that you should scan quarterly and patch within 30 days of vulnerability release, respectively; however, these are lower bounds for meeting compliance standards. The minimum scanning frequency an organization can achieve depends not only on the size and of the technology environment to be scanned, but also on the processing overhead defined around the scan.
Vulnerability scans are usually performed during non-business hours to minimize potential impacts and it's good practice that the scans do not compete with other resource-intensive activities (backups and file transfers). As with any other activity running during off-hours, the availability of resources for support and troubleshooting should be planned. In highly regulated IT environments, coordinating the scans with change management processes is an important requirement.
The best way to prioritize vulnerabilities is based on the associated security risk posed to the organization. A good framework for vulnerability prioritization has four components that fall into two categories — vulnerability context and asset context.
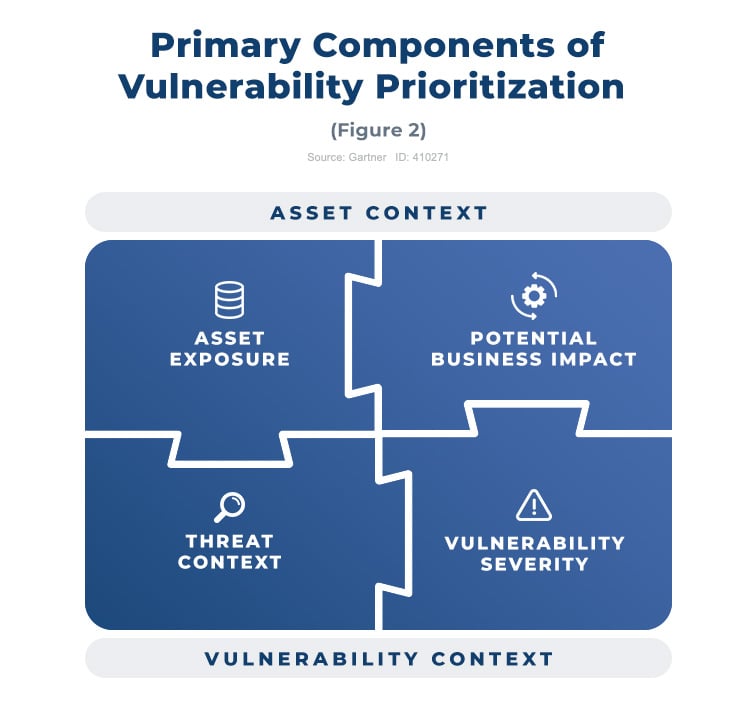
The definition of a prioritization method depends on a few factors, ranging from the complexity of the environment to the context data available. It is important to remember that prioritization approaches and the data that fuels them must be re-evaluated from time to time (prioritize risk proactively and reactively). The following are the most useful methods:
Organizations often produce a prioritization model based on a combination of factors and the decision of which factors to use is based on multiple aspects, including the availability of data, granularity provided, required tools, and amount of effort involved in applying the resulting criteria.
Some technologies are recommended for organizations that want to simplify their prioritization efforts; modern vulnerability assessment and Risk-Based Vulnerability Management (RBVM) vendors are pioneering the evolution of VM with the dynamic addition of threat data to the prioritization process. They are also leveraging more sophisticated scoring methodologies, including predictive models for vulnerability exploitation. The VA vendors themselves are also expanding their products to include RBVM capabilities.
In the next articles of the series, we will talk about the remediation of vulnerabilities.
| Column Header Text | Column Header Text | Column Header Text |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
|
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Performing a review of the media inventories at least annually |
Performing a review of the media inventories at least annually |
Performing a review of the media inventories at least annually |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
 Image caption goes here. This is HTML text.
Image caption goes here. This is HTML text.
Established in 2009, Advantio offers a comprehensive portfolio of professional, managed, advisory, and security testing services. Our subject matter expertise and services focus on cybersecurity, data protection, risk, and compliance with a distinct specialization in the ‘Payment Card Industry.’ We believe that for your organization to compete and grow in a rapidly evolving environment, investing in the right partner and technology is crucial to help you focus better on your core business. Our team works tirelessly to help you achieve, maintain, and demonstrate compliance against the most demanding cybersecurity standards and regulatory frameworks on time and on budget. With a strong presence across Europe and global reach on four continents, we have become the partner of choice for many large corporates and international enterprises. Our clients span a diverse range of fintech suppliers and fintech consumers in verticals such as travel, hospitality, telecommunication, financial, healthcare, education, entertainment, government, non-profit and more.
Comments