Any business processing online card payments and willing to maintain customer security should have come into 3D Secure, Visa’s and MasterCard’s anti-fraud card verification program. 3D Secure service is provided by Visa and MasterCard under the name Verified by Visa and MasterCard SecureCode, respectively. But as technology evolves, payment brands are rolling out 3D Secure 2.0 (3DS 2.0).This new protocol is designed to be faster and more secure, protecting every entity involved in an online transaction. Perhaps the most important improvement is for the paying customer. By using contextual information about the transaction, 3D Secure 2.0 is designed to overcome the biggest complaint about v1.0 – having to enter a password to verify the transaction.
EMVCo, the payment standards body responsible for administering 3DS, claim that checkout time is reduced by 85% using the new protocol.
v2.0 is more than a cosmetic update however; organizations involved in handling online card payments will need to re-verify their 3DS compliance.
Who needs to be v2.0 validated?
There are three key entities who will need to be 3D Secure 2.0 validated:
- Access Control Server (ACS) providers
- Directory Server (DS) providers
- 3DS Server (3DSS) providers
In reality, most entities falling into these categories will already hold some form of validation. But it is extremely important to note that there are distinct differences between 3DS protocols and, accordingly, between validation requirements. The Verified by Visa (VbV) standard is definitely not the same as the PCI 3DS standard.
Almost everything has changed
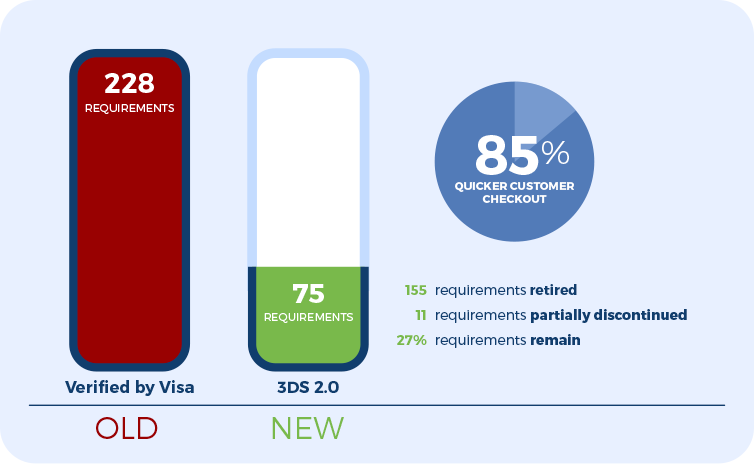 Of the 228 requirements for Verified by Visa compliance, 155 have been retired (68%) and 11 are partially discontinued (5%). This leaves just one quarter (27%) of existing requirements in place.
Of the 228 requirements for Verified by Visa compliance, 155 have been retired (68%) and 11 are partially discontinued (5%). This leaves just one quarter (27%) of existing requirements in place.
In theory, 3DS 2.0 compliance should be much easier to achieve. There are just 75 requirements, and less than half (44%) are new. But the actual onsite assessment and reporting process may be longer than with VbV. This is due to the fact that the reporting process defined by the PCI SSC requires much more assessment details to be documented.
It is important to note that the acceptance testing process has also changed somewhat. Acceptance testing is now overseen by EMVCo, and entities will need an approval letter from this new body before PCI 3DS assessment. And since July 2018, 3DS 1.0 environments must be assessed against the 2.0 specification in order to achieve PCI 3DS compliance.
Problems you will face working towards PCI 3DS 2.0 compliance
For any 1.0 compliant organization, the first hurdle is choosing a Qualified Security Assessor (QSA) to test payment handling systems. To ensure high standards are maintained at all times, QSAs are not permitted to revalidate the same entity for more than two consecutive years. Some QSAs may receive explicit permission from Visa to override this requirement. This is issued on a case-by-case basis, and your organization should assume that such permission will not be granted.
Other issues are far more technical in nature. Existing systems may retain sensitive 3DS data (such as the payment card’s 3DS verification value) where not required. This would demonstrate an instant compliance failure, so systems will need to be updated to prevent these incidents.
Another common problem is the way in which legitimate data is stored. Sensitive data defined in the PCI 3DS matrix, such as HTML templates, are saved without appropriate encryption, or not securely deleted when no longer required.
Entities are also expected to provide additional monitoring and oversight under PCI 3DS 2.0. Transactions must be monitored for signs of anomalous activity to reduce instances of fraud. Obviously, the development and deployment of proactive analysis is costly and time-consuming but it is also unavoidable.
There are physical challenges that need to be addressed too. PCI DSS requirements make no provisions for physical security safeguards in the data center. But, 3DS expects the use of mechanisms like single-man traps to control access to server rooms for instance. This may involve infrastructure upgrades to achieve compliance.
Similarly, hardware security modules (HSM) are not new but the way in which encryption keys are handled has changed. Access to HSMs must be managed using dual control to ensure no single party has access to all of the relevant encryption keys.
Perhaps most challenging of all is the current compliance status of Cloud platforms that many entities rely on. The Key Management Service (KMS) HSM used by Amazon Web Services (AWS) is based on FIPS 140-2 Level 2; 3DS 2.0 compliance demands Level 3 support for instance. The HSM remote access utility is similarly lacking. Without achieving ISO 13491 compliance, it will not be acceptable for use in a PCI 3DS 2.0 payment system either.
AWS users will need to lobby Amazon hard to demand the required technology stack upgrade or plan a migration to an alternative platform. Without proof that physical security and HSM protection measures are up to the 3DS standard, the platform is unsuitable for entities looking to build compliant platform.
Can’t we just retain our 1.0 compliant systems?
Given that achieving 3DS 2.0 compliance will require significant additional investment, entities may be tempted to retain their existing 1.0 compliant systems. This is not a realistic option.
First, the fact that 1.0-based systems will now be assessed using the 2.0 criteria means that many systems will fail security checks, even though they meet the standards that were relevant at the time of deployment. Second, in order to better protect their customers, merchants are demanding that service providers accelerate 3DS 2.0 uptake.
Ultimately, 3DS 2.0 does deliver benefits; by making transactions more powerful, flexible and secure, providers are able to offer customers a better quality of service. And this means it will help to increase the average order value and encourage repeat business.
Despite 3DS 2.0 compliance being managed by EMVCo, the organization is owned by the major payment brands (Visa, American Express, Discover, JCB, MasterCard and UnionPay). These brands set the rules, and they are pushing hard for issuers and acquirers to adopt the standard. Ultimately, any firm that cannot prove 2.0 compliance is unlikely to be allowed to process payments in the near future.
To avoid these problems, and to ensure PCI 3DS 2.0 compliance, entities will need to act sooner rather than later. To discuss your options and how Advantio can help you achieve the necessary security standards, please get in touch.