Visa Europe revealed important stats about the usage of Contactless Cards. Poland, Spain and the UK use this payment methd the most, with UK usage growing by 300% year over year.
Visa Europe revealed important stats about the usage of Contactless Cards. Poland, Spain and the UK use this payment methd the most, with UK usage growing by 300% year over year.

In July 480 B.C., the great Persian army conquered the Greek city-states on its way south, and soon all of northern Greece would be surrendered. In order for the small Spartan army to successfully resist, it needed a narrow space to which the large Persian army could only send small contingents. Such a place existed: it was the pass of Thermopylae; there the Spartans steadfastly defended the strait on an equal footing as the days passed and Xerxes despaired. But then the Persians, with the help of a traitor, discovered a narrow road leading through the mountain to the other side of Thermopylae, thus trapping the Greeks from their rear.
Some 2,400 years later, in the early 1930s, France, the winner of the so-called Great War, fearful of the threat posed by the growing uprising of National Socialism on its northern border, would give impetus to the construction of the Maginot Line: a series of static defensive fortifications on the border with Germany and Italy. When, in May 1940, Nazi Germany decided to invade France, it would do so with its main force through the forested area of the Ardennes in Belgium, which had been considered by the French to be impassable to armored forces, thus managing to reach the rear of the Allied army.
It has not been rare in history, that a situation or supposedly advantageous element turns out to be ineffective either due to unusual or unexpected scenarios, and that therefore have not been controlled (in risk management, it is known as the "black swan" theory) or simply due to bad implementations or as a result of compromise solutions.
In order to protect publicly exposed websites, web applications or APIs from attacks, most companies choose to deploy a Web Application Firewall (WAF), so that any attempt at attack is blocked before it materializes.
The main functionality of WAFs is the filtering, monitoring and transformation (decoding and sanitization) of HTTP traffic, operating at layer 7 of the OSI model, unlike a traditional network firewall that operates at layers 3 and 4 since it is only capable of inspecting IP packets of the TCP/UDP protocols in order to filter by IP address, port and protocol.
This HTTP traffic processed in the WAF is inspected using a set of rules or policies to detect a particular type of attack such as those identified in the OWASP Top 10 or CWE Top 25: Cross-Site-Scripting (XSS), SQL injection, Insecure De-Serialization, Cross-Site Request Forgery (CSRF), Unvalidated Redirects and Forwards and many more.
Among the recommendations and good practices of the industry, Payment Card Industry (PCI) Data Security Standard stands out, which in its requirement 6.6 indicates us:
“For public web applications, continuously address new threats and vulnerabilities and ensure that these applications are protected against known attacks using one of the following methods: …
- Installation of an automatic technical solution that detects and prevents web attacks (e.g. web application firewall) in front of public web applications in order to control traffic continuously".
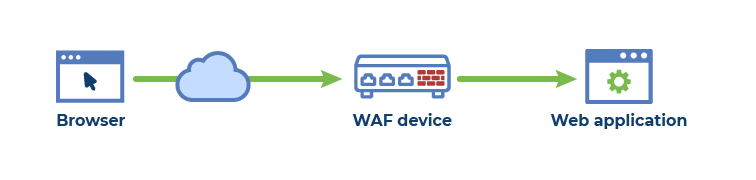
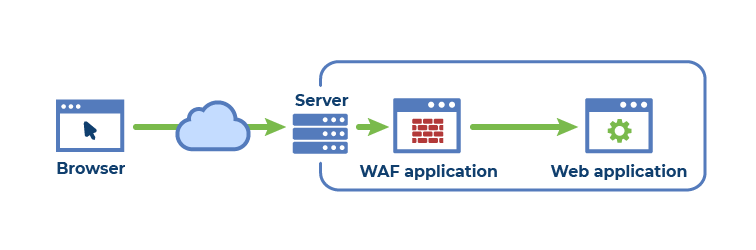
At present, a WAF can be deployed at several levels according to its typology:
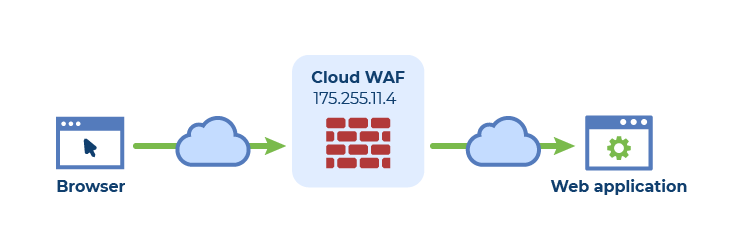
The adoption of cloud solutions is clearly on the rise in recent years to the detriment of other solutions, motivated by the great advantages it offers:
There are many providers that offer some kind of more or less complex WAF service in the cloud, some of the best known are Cloudflare, Akamai, F5, Amazon Web Services, Microsoft Azure, etc.
When we proceed to add a WAF cloud to our environment, we usually follow these general steps:
In general, with these steps we would already have a WAF deployed at the front of the website, web application or API; however, this is not always true: if access is not made by DNS resolution of the domain, anyone who knew the original IP could attack it without their traffic being intercepted and sanctioned by the WAF:
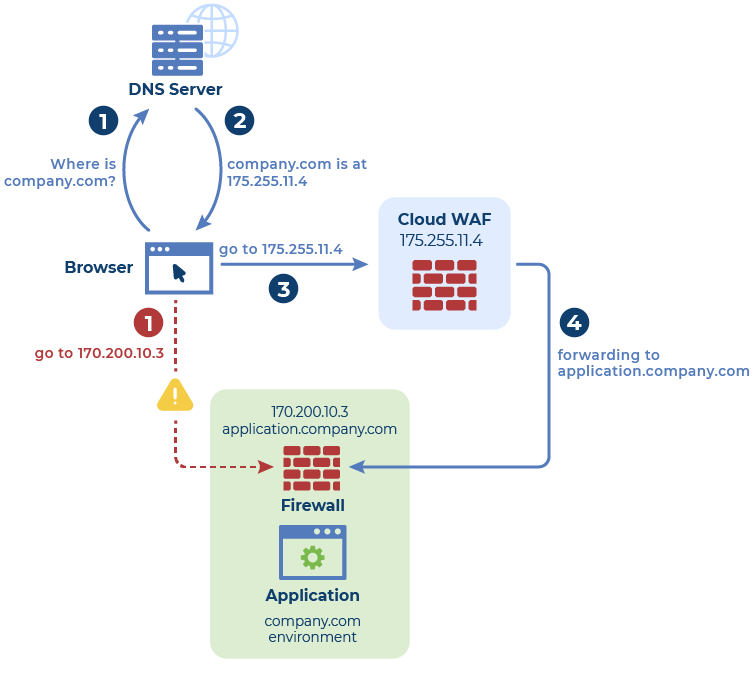
The problem usually arises when, after a previous publicly exposed environment, we perform the steps mentioned above and leave access to the original IP unrestricted.
Firstly, a hypothetical attacker would try to identify the presence of a WAF that could alert and prevent his intrusion attempts; to do so, identification tools as common as the following are usually used:
When the identification of the WAF is positive, is when the potential attacker will try to identify which is the original IP of our server before devoting efforts in much more complex techniques of evasion.
For the enumeration of server IPs after the WAF, it is very common for the attacker to employ tools such as the following:
Once the attacker has identified the original IPs in our environment, these will become the main attack vector as they are less protected.
For all these reasons, in order to limit the exposure of these weak points of the environment, it is essential to carry out some kind of protection or strict limitation of access to the original IPs only from the services of the Cloud WAF, via firewalling rules that limit the IPs or domains of incoming connections.
| Column Header Text | Column Header Text | Column Header Text |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
|
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Their work should have not stopped there because achieving compliance is an occasional result that doesn't ensure a continual protection. |
Performing a review of the media inventories at least annually |
Performing a review of the media inventories at least annually |
Performing a review of the media inventories at least annually |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
Row Header Text |
Lorem ipsum dolor sit |
Lorem ipsum dolor sit |
23 |
 Image caption goes here. This is HTML text.
Image caption goes here. This is HTML text.
I am the Senior Security Consultant in Advantio. I have more than 10 years of experience working mainly in the Spanish market. My information security background includes system administration, consultancy, risk advisory services for technology, compliance and legal, design and development of documental frameworks, among others.
CISM, CISA, CRISC, PCI QSA, QSA (P2PE), ISO 22301 LA, ITIL F
Comments